Crypto Report #0134.4 Undeads.com routed ~$1M through OFAC-sanctioned Cryptex.net while its investors n0b0dy.eth and indifferent.eth received funds from the same mixer
[!IMPORTANT] The report is part of a big invesgation Crypto Report #0134 Stolen 100 ETHs Leads to NFT Whales n0b0dy and indifferentguy (25mln$ worth) and a real company undeads.com (6mln$ investments and 50mln$ coin cap).
Keywords
crypto laundering, Cryptex.net, OFAC sanctions, indifferent.eth, indifferentguy.eth, n0b0dy.eth, undeads.com, UndeadsMysteryBox, Binance, money laundering, CryptexPay, sanctioned exchange, crypto mixer, crypto report, crypto investigation
Statements from related investigations
-
n0b0dy.eth and indifferent.eth are managed by a single person or a coordinated group - Report #0134.0
-
Undeads.com has been funded with illicit money provided by investors n0b0dy.eth and indifferent.eth - Report #0134.1
-
n0b0dy.eth tries to hide the information about funding into Undeads.com - Report #0134.1
-
A single individual or a coordinated group controls roughly 40% of the unlocked $UDS market capitalization - Report #0134.3
Abstract
-
n0b0dy.eth and indifferent.eth used Cryptex.net - a platform known for facilitating anonymous cryptocurrency transactions.
-
On-chain evidence shows that stolen ETH and other assets were routed through Cryptex.net before being redistributed to wallets controlled by n0b0dy.eth and indifferent.eth.
-
Between March and May 2023, Undeads.com transferred a total of 540 ETH (~$970,000 at spring 2023 prices) to intermediary wallets that forwarded the funds to Cryptex.net hot wallets and Binance.
-
The use of Cryptex.net as an intermediary demonstrates a deliberate attempt to obscure the origin of illicit funds.
What is Cryptex.net
Cryptex.net was a cryptocurrency exchange registered in Saint Vincent and the Grenadines but predominantly operating within Russia. On September 26, 2024, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) sanctioned Cryptex under Executive Orders 13694 and 14024, designating it as a major money laundering platform.
Key facts about Cryptex:
- Processed over $5.88 billion in cryptocurrency transactions over its lifetime
- Received more than $51.2 million in funds derived from ransomware attacks
- Associated with over $720 million in transactions connected to Russia-based ransomware actors, fraud shops, mixing services, and darknet markets
- Operated by Sergey Sergeevich Ivanov (also known as “Taleon”), a Russian money launderer who processed hundreds of millions of dollars for cybercriminals over approximately 20 years
- The U.S. Department of State offered a $10 million reward for information leading to Ivanov’s arrest or conviction
- Cryptex’s payment processor, CryptexPay, employed advanced obfuscation by generating new wallet addresses for each transaction and mixing deposits - making it extremely difficult for authorities to trace criminal proceeds
- Dutch authorities (FIOD and NHCTU), coordinating with the U.S. Secret Service, seized Cryptex’s infrastructure and domains, recovering €7 million in cryptocurrency from servers hosted in the Netherlands
- The Netherlands Police, the Dutch Fiscal Intelligence and Investigation Service (FIOD), and the German Federal Criminal Police (BKA), as part of Operation Endgame, provided substantial assistance in the case
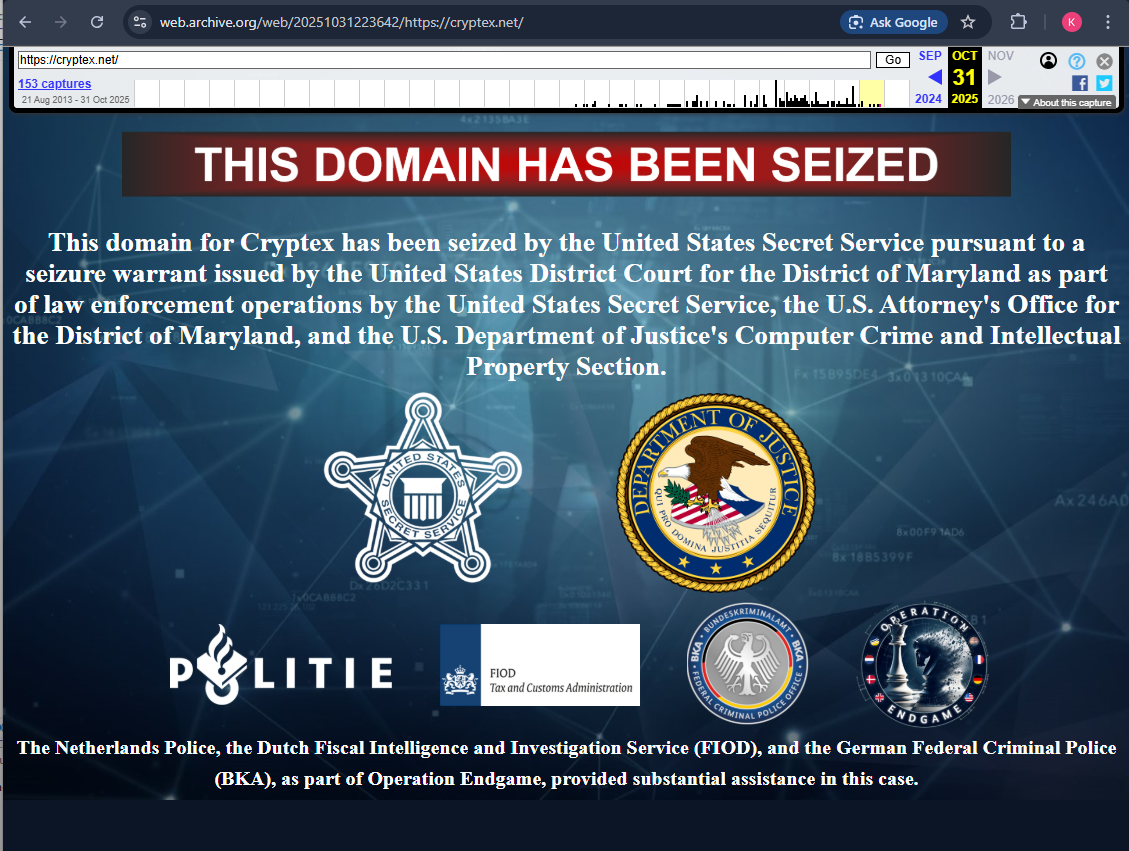
Source: web.archive.org snapshot of cryptex.net showing the seizure warrant issued by the United States District Court for the District of Maryland.
Money laundering via Cryptex.net
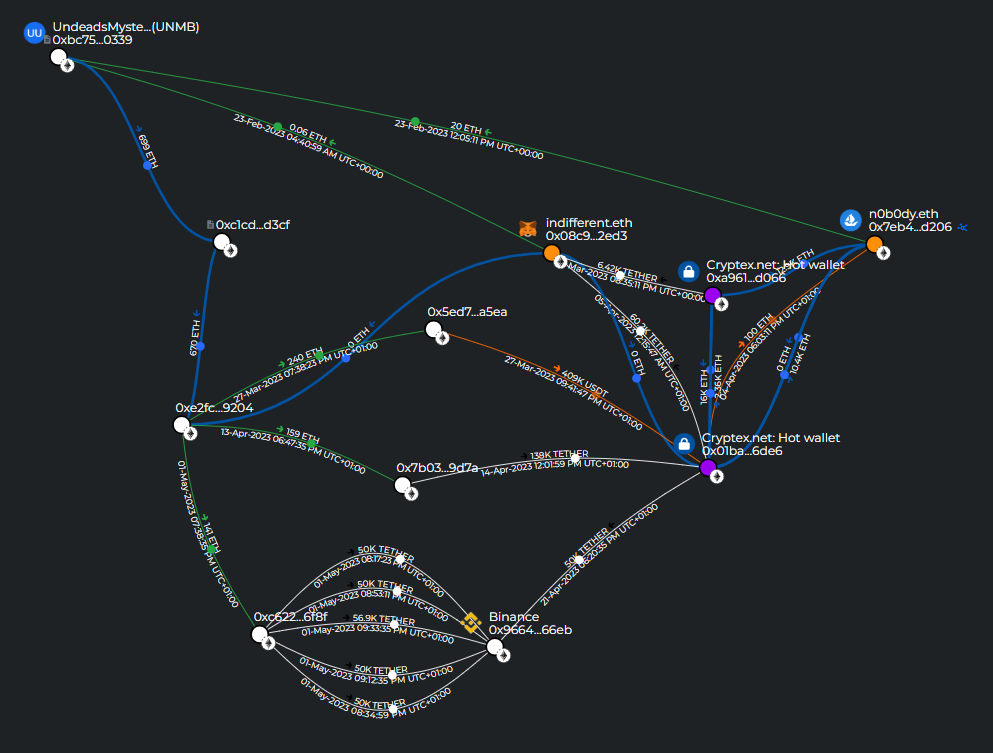
The on-chain investigation reveals that wallets associated with n0b0dy.eth and indifferent.eth interacted with Cryptex.net to process and obscure the origin of funds.
Specifically, n0b0dy.eth and indifferent.eth used two Cryptex.net hot wallets:
- 0xa9615dfa74c79b38ee144169b5e87dfba43ed066 (Etherscan)
- 0x01baea860c7661561c31b1f765cfe8e064ff6de6 (Etherscan)
The Breadcrumbs report visualizes the flow of funds between the investigated wallets and Cryptex: https://www.breadcrumbs.app/reports/39217?share=18e383c8-dbe7-4c72-8084-e2ec3c962d6e
On-chain evidence
The on-chain transaction data reveals multiple transactions between 11 wallets during February–May 2023, tracing the full laundering cycle from Cryptex.net through n0b0dy.eth and indifferent.eth to Undeads.com and Binance.
Wallets involved
| Address | Identity |
|---|---|
| 0x7eb413211a9de1cd2fe8b8bb6055636c43f7d206 | n0b0dy.eth |
| 0x08c904a02578ed95a46c25a8cc510cd6ed9f2ed3 | indifferent.eth |
| 0xa9615dfa74c79b38ee144169b5e87dfba43ed066 | Cryptex.net hot wallet #1 |
| 0x01baea860c7661561c31b1f765cfe8e064ff6de6 | Cryptex.net hot wallet #2 |
| 0xbc75da5ad73edf07b1dd38c4b158f45318f30339 | UndeadsMysteryBox (UNMB) - Undeads.com wallet |
| 0x9664465588585758823b4b49079cc668097f66eb | Binance Deposit Wallet |
| 0xe2fc8fcae91f0bb046367d198861731a068a9204 | Undeads.com wallet |
| 0xc1cd80849b138909c5599096c0cab36c229ed3cf | Undeads.com TransparentUpgradeableProxy (smart contract) |
| 0x5ed706e051605df8b58844572fa3cf16d2eda5ea | Intermediary wallet |
| 0x7b03a5d14332b4111ee839f8956f7efe31b69d7a | Intermediary wallet |
| 0xc622a675cf2bccc88162e777a1f3e0a275f96f8f | Intermediary wallet |
[!NOTE] By May 2023, n0b0dy.eth and indifferent.eth had received funds from two Cryptex.net hot wallets: ~90K USDT to indifferent.eth and ~23K ETH to n0b0dy.eth. See the full Breadcrumbs report for details.
Step 1: n0b0dy.eth and indifferent.eth fund the Undeads.com wallet (February 23, 2023)
On February 23, 2023, n0b0dy.eth sent 20 ETH to the UndeadsMysteryBox (UNMB) wallet (0xbc75...39):
0x64fbef3a556c176d5b3c947b080e4dcec619a4ca00510f64fa7ce3f6f897e38c
On February 23, 2023, indifferent.eth sent 0.06 ETH to the same UndeadsMysteryBox (UNMB) wallet (0xbc75...39):
0xb5d198c43334b88ce314207bee190fa244166208850eff23f67d2b64798d4efe
[!NOTE] Both n0b0dy.eth and indifferent.eth sent funds to the same Undeads.com wallet (UndeadsMysteryBox) at the same date, further confirming the direct financial relationship between these wallets and the Undeads.com project.
Step 2: Undeads.com wallet sends funds to Cryptex via intermediary (March 27, 2023)
- March 27, 2023: Undeads.com (
0xe2fc...04) → intermediary (0x5ed7...ea): 240 ETH (tx) - March 27, 2023: Intermediary (
0x5ed7...ea) → Cryptex hot wallet #2: 409,245 USDT (tx)
Step 3: Cryptex.net sends funds to n0b0dy.eth and indifferent.eth (April 4–5, 2023)
On April 4, 2023, Cryptex hot wallet #2 sent 100 ETH to n0b0dy.eth (0x7eb4...06):
0xe82d496d785c6dbb8ef5c106a9b2a0b47c2a9be25ba61d944a438def999f0543
On April 5, 2023, Cryptex hot wallet #2 sent 60,222 USDT to indifferent.eth (0x08c9...d3):
0x4f047877cc2fc94d4dd55ed9f12ebcc2e6b00c7c81f1345c2e09494f2a04eee7
Step 4: Undeads.com wallet sends funds to Cryptex and Binance via intermediaries (April 13–21, 2023)
- April 13, 2023: Undeads.com (
0xe2fc...04) → intermediary (0x7b03...7a): 159 ETH (tx) - April 14, 2023: Intermediary (
0x7b03...7a) → Cryptex hot wallet #2: 138,083 USDT (tx) - April 21, 2023: Cryptex hot wallet #2 → Binance: 50,000 USDT (tx)
Step 5: Undeads.com wallet routes funds through intermediary to Binance (May 1, 2023)
- May 1, 2023: Undeads.com (
0xe2fc...04) → intermediary (0xc622...8f): 141 ETH (tx) - May 1, 2023: Intermediary (
0xc622...8f) → Binance: 5 transactions totaling 256,946 USDT (tx1, tx2, tx3, tx4, tx5)
Summary
In total, the Undeads.com wallet (0xe2fc...04) sent 540 ETH (~$970,000 at spring 2023 ETH prices) to three intermediary wallets that forwarded the funds to Cryptex.net and Binance. The intermediaries forwarded 409,245 USDT and 138,083 USDT to Cryptex hot wallet #2. The Binance deposit wallet received approximately 306,946 USDT across 6 transactions. This means Undeads.com itself was directly involved in routing funds through the Cryptex laundering infrastructure and into Binance - not just a passive recipient of laundered investments.
The closed-loop laundering pattern
The on-chain data reveals a striking closed-loop money laundering cycle - with Undeads.com wallets appearing at both ends of the Cryptex.net pipeline:
- n0b0dy.eth / indifferent.eth → Undeads.com: Both wallets send funds to the UndeadsMysteryBox (UNMB) wallet - directly funding Undeads.com with money received from a sanctioned laundering platform
- Undeads.com → Cryptex: The Undeads.com wallet (
0xe2fc...04) sends 540 ETH (~$970,000) through intermediaries to Cryptex hot wallet #2. The intermediaries forward 409,245 USDT and 138,083 USDT to Cryptex - Cryptex → n0b0dy.eth / indifferent.eth: Cryptex hot wallets send ~23K USDT to n0b0dy.eth and ~90K USDT to indifferent.eth
- Cryptex / intermediaries → Binance: Funds are deposited into a Binance Deposit Wallet - approximately 306,946 USDT across 6 transactions - consistent with cashing out laundered funds
The loop can be visualized as:
┌──────────────────────────────────────────────────────────┐
│ │
▼ │
Cryptex.net ──► n0b0dy.eth / indifferent.eth ──► Undeads.com ─┘
│ (UndeadsMysteryBox)
│
└──► Intermediaries ──► Binance (cash-out)
This circular flow of funds between Cryptex.net, n0b0dy.eth/indifferent.eth, and Undeads.com is a hallmark of money laundering - funds are cycled through multiple entities to obscure their origin, with a sanctioned mixing platform at the center of the loop.
[!IMPORTANT] The presence of an Undeads.com wallet (
0xe2fc...04) as a source of funds flowing into Cryptex.net is critical. This means Undeads.com was not merely a passive recipient of laundered investments - the project’s own wallets were actively routing funds through a sanctioned money laundering platform and back through the same network of wallets, forming a closed laundering loop.
Connection to the broader investigation
The previous reports in this investigation established that:
- n0b0dy.eth and indifferent.eth invested millions into Undeads.com during pre-seed and seed rounds
- Undeads.com hides its legal entity information intentionally
- n0b0dy.eth and indifferent.eth control roughly 40% of the unlocked $UDS market cap
The discovery that these wallets also used Cryptex.net - a platform sanctioned by OFAC specifically for facilitating money laundering - and that funds flowed directly from Cryptex to both n0b0dy.eth/indifferent.eth and the Undeads.com wallet, adds critical evidence that the funds flowing through these entities are of illicit origin.
Conclusions
-
n0b0dy.eth and indifferent.eth received funds directly from Cryptex.net hot wallets - a cryptocurrency exchange sanctioned by OFAC on September 26, 2024 and seized by the United States Secret Service.
-
Cryptex.net was not a regular exchange. It was a platform specifically designed for money laundering, processing over $720 million in transactions linked to ransomware actors and cybercriminals, and was operated by a sanctioned Russian money launderer.
-
Both n0b0dy.eth and indifferent.eth sent funds to the same Undeads.com wallet (UndeadsMysteryBox -
0xbc75...39), directly confirming that Undeads.com received money that passed through a sanctioned laundering platform. -
An Undeads.com wallet (
0xe2fc...04) was itself a source of funds flowing into Cryptex.net through intermediaries - including 409,245 USDT and 138,083 USDT. This proves Undeads.com was not merely a passive recipient of laundered funds, but actively participated in routing money through a sanctioned laundering platform. -
Large amounts were subsequently deposited into a Binance Deposit Wallet (
0x9664...eb) - approximately 306,946 USDT across 6 transactions - consistent with cashing out laundered funds through a major exchange. -
The on-chain evidence reveals a bidirectional laundering cycle: Cryptex.net ↔ n0b0dy.eth / indifferent.eth ↔ Undeads.com → Binance. This is not a coincidental use of a later-sanctioned service - it is a deliberate money laundering operation involving the Undeads.com project itself.
Related Wallets
0x7eb413211a9de1cd2fe8b8bb6055636c43f7d206
0x08c904a02578ed95a46c25a8cc510cd6ed9f2ed3
0xa9615dfa74c79b38ee144169b5e87dfba43ed066
0x01baea860c7661561c31b1f765cfe8e064ff6de6
0xbc75da5ad73edf07b1dd38c4b158f45318f30339
0x9664465588585758823b4b49079cc668097f66eb
0xe2fc8fcae91f0bb046367d198861731a068a9204
0xc1cd80849b138909c5599096c0cab36c229ed3cf
0x5ed706e051605df8b58844572fa3cf16d2eda5ea
0x7b03a5d14332b4111ee839f8956f7efe31b69d7a
0xc622a675cf2bccc88162e777a1f3e0a275f96f8f
Images
[!IMPORTANT] For any further clarification regarding the current investigation, please contact @cryptokarl013. Any assistance that helps enrich the investigation would be greatly appreciated.
The report’s content is based on verifiable public information.